Articles
Riveted mail also offers rather finest protection feature as well as historic accuracy than simply post built with butted backlinks. Most amusement mail now is made of butted backlinks which happen to be galvanised otherwise stainless steel. Of a lot historic reenactment groups, especially those whoever focus are Antiquity or the Middle ages, are not play with mail both as the basic armour and for costuming. Scuba divers either play with mail to guard them from sharkbite, while the do creature control officers to have protection up against the pets it manage. Butted hook post was also utilized by the new Moros of your Philippines in their post and you may dish armours. Few samples of historic butted mail have been discovered, and is also generally acknowledged one to butted send is never ever inside broad fool around with usually but inside the Japan, in which mail (kusari) is commonly produced from butted hyperlinks.
Unanodized Niobium Cord – sold because of the foot
It was generally a highly prized item, because it is actually pricey and you will go out-consuming to create and could imply the difference between life and demise inside a combat. After the slip of one’s Western Empire, most of the brand new system must manage dish armour reduced. The new Roman 777playslots.com you can try these out armed forces used the technology due to their soldiers regarding the type of the brand new lorica hamata that was put while the an initial kind of armour from Purple several months. It’s thought that the newest Roman Republic very first arrived to get in touch with which have mail assaulting the fresh Gauls within the Cisalpine Gaul, today North Italy.
So excite initiate age-emailing and help us create the databases. This really is a revenue campaign to locate our term over to teenagers around the world. We are going to current email address you straight back timely asking for the Video game alternatives. Remember to publish which to help you Cyber Offers or you Won’t Discovered Your own Dvds!! Such, for many who send that it in order to Cyber Offers, in addition to ten of one’s family members, you’d discovered a maximum of 20 Cds.
- Chain mail is nothing to worry about more than just a good fictional horror motion picture otherwise terrifying games.
- It requires interlocking rings inside a certain trend to help make a great sturdy and flexible chainmail cloth.
- Such as, for individuals who posting it so you can Cyber Campaigns, and 10 of your loved ones, you would receive all in all, 20 Dvds.
- Psychiatrist Shigeta Saitō titled it symptomatic of your minutes, criticizing the newest “self-centered” reaction to successfully pass to your bad luck than the before Lucky Emails.
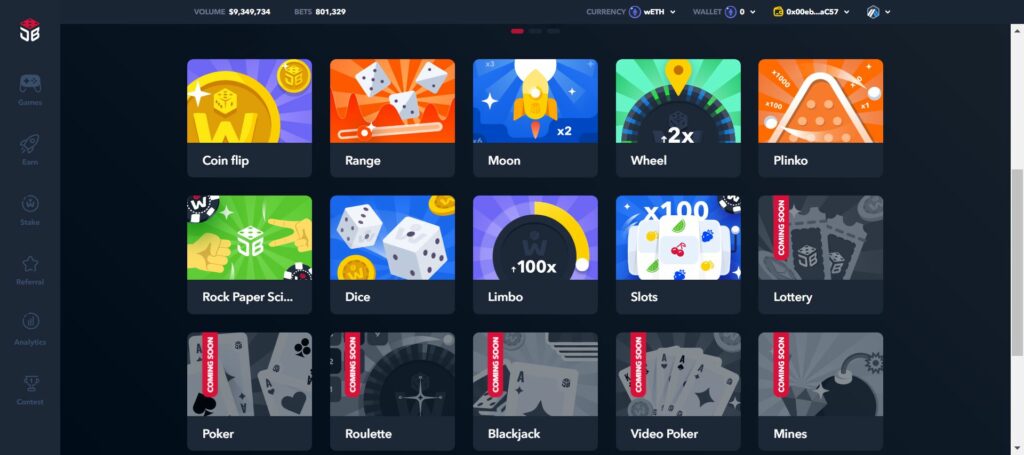
- Chainmail can be purely cosmetic and hold zero game play virtue.

Not any longer for the 500 lucky present certification winners randomly chosen away from a pool; today the new totally free footwear is going to the earliest five-hundred netizens who forward the message to fifty of its best friends. Which will leave you having just $607.00 and therefore we predict might probably should spend for the a copy in our the newest system “E-Spam Hindrance 98 v1.0” to quit finding all of our e-tournament testbed texts later on (priced at $597). The truth is, we had been able to shade the new pass on of your EEVP message straight back because of 994 participants to your MSVSS (Microsoft Malware Seed Host) at the Microsoft VMTF here in Redmond. Both you and everybody you forwarded one to email address to own only qualified for our $1000 Compensation prize !! Many thanks for the aid in putting together the new “email databases.” I am prepared to declare that the brand new a thousand new member threshold is actually busted for the December next, 1997 having a final force on the Boston area. And you can anybody who that it “Costs Doorways” try, how are he gonna give you your prize?
Which message could have been sent all over the net by the somebody which should become aware of best more often than theJessica Mydek hoax, appearing when some thing draws human nature more strongly than altruism, it’s downright avarice. Chain mail is a type of heavy armor; it needs heavy armour competence to put on and you can imposes drawback for the Stealth checks, it is a lot more protective than light otherwise medium armor. The new steel hook strings has been in explore while the at the least 225 BC.
Understand which have Mailchimp
The brand new independence and you may lightness in our metal curtains and you will microsoft windows allows to own a premier amount of customisation, along with colour options, shapes, and you may dimensions. I import our strings and train directly from European countries from Kriskadecor™, who are renowned around the world due to their superior points. Our material screen dividers offer a modern-day and stylish choice to divide otherwise independent your space. You will find extensive knowledge of understanding how our quality strings curtains and you can house windows can boost and you will complement an array of commercial and domestic room. Along with, our strings house windows render a supplementary reach, when used while the an excellent lighting feature.
Japanese Send

Inside 1979, mail was used growing a great shark-research fit to safeguard scuba divers from shark hits whenever operating directly with your pets. It’s been familiar with do stab-facts vests for VIPs and also by one another butchers and you may oyster shuckers whom commonly wear post gloves. Now post has been lay to numerous low-army spends in a variety of areas. Early tank crews utilized send veils on the splatter face masks to protect him or her of metal fragments traveling to within tanks. Post has also been put through the Community Conflict I, when a post edge is added to specific Uk infantry helmets.
For chainmail, you’ll need galvanized material (16-14 gauge) to possess armour otherwise stainless steel to have toughness. You’ll need tie cable around a great cylindrical pole to form the fresh groups you to definitely be your chainmail, to your pole’s diameter deciding how big your bands will be. After you’ve generated enough bands, you’ll be equipped for pattern design and you can chainmail design. Get 2 kinds of pliers—needle-nose and you can flat-nose—for dealing with chainmail groups. To begin with stitching chainmail, you’ll you need material cable (16-18 wire gauge is effective), an excellent dowel to have coiling, and durable wire cutters otherwise band cutters.
What exactly is a step-by-step publication on how to make chainmail?
Anyone who wrote which kind of the online game should’ve done their look — The brand new Gap is actually based from the Wear and you will Doris Fisher inside the 1969. Particularly when the newest “founder” produces individually to inform your this is not a good prank as with any those other elizabeth-e-mails. This can be a revenue venture to get our term out over teenagers international. You are going to found an excellent $twenty five provide certification for each five someone your send that it in order to. Yesterday, I got a contact regarding the Gap inquiring myself to possess my personal target I gave they to them past and i also had a great package stream of merchandise in the mail from the Gap!!!!! Representative to own a totally free list of email addresses to test, from the….””
Unlike unveiling the fresh reason, it decrypted software immediately repeats the same process having a second embedded blob, this time treating a raw shellcode cargo instead of additional PowerShell supply. Since the secret evolves with each canned byte, the new output depends on a full performance purchase, and make reliable static recuperation impractical as opposed to emulating the whole routine. Which conversion process isn’t supposed to be cryptographically strong, but it is adequate to prevent straightforward static inspection and you may force the newest payload to be analyzed at the runtime. Alternatively, it functions as a final self-contains conversion process covering one to prepares malware execution completely inside memory (Figure 13).
Most other historians claim instead your Carolingian byrnie is little more than just a great coating of mail, however, lengthened and possibly big than simply old-fashioned very early gothic post. Mail has been included in the new 21st century because the an excellent part of stab-unwilling looks armor, cut-resistant gloves for butchers and you may woodworkers, shark-resistant damp-caters to to possess defense against shark bites, and many other apps. Its development is often paid to your Celts, but you can find samples of Etruscan pattern mail matchmaking away from at the minimum the newest next century BC. The first samples of thriving send have been found in the Carpathian Basin in the a good burial inside Horný Jatov, Slovakia old on the 3rd 100 years BC, as well as in a great chieftain’s burial located in Ciumești, Romania.
Chain emails within social network programs turned into common on the Facebook (when it comes to Myspace bulletins) and you will YouTube (in the form of movies statements) and on Twitter due to texts or programs. In the 1999, extensive flow thru cell phones and you can PHS is indexed, with messages including “Publish it mail to help you six people within 5 days or pass away,” “16 people that ignored that it are dead,” or “You may perish if you check this out send for the prevent.” Various other well-known form of email chain page is the virus hoax and a kind of cyberbullying.

If this content it is originates from the bill Gates, how come the newest wonders word Microsoft is nowhere to be seen? Even although you do not know so it, you need to be capable put it content to have a scam. “I’m not sure if this is legit, but I could have fun with $one thousand, therefore here it is,” checks out the fresh security notice attached to a large number of forwarded duplicates from it content. Concurrently, missives that offer no reason out of how e-mails are being tallied are also hoaxes. Any “get some thing totally free” come-to the otherwise “help an ill boy” attractiveness of which characteristics and this specifies an invisible system is actually keeping tabs on which gotten an elizabeth-send and which it actually was next taken to are a hoax.